I'll lead from the roots with the etymology of person :
person (n.)
from Latin persona "human being, person, personage; a part in a drama, assumed character," originally "a mask, a false face," such as those of wood or clay, covering the whole head, worn by the actors in later Roman theater. OED offers the general 19c. explanation of persona as "related to" Latin personare "to sound through" (i.e. the mask as something spoken through and perhaps amplifying the voice).
Armed thusly and proceeding with arete, the questions are : how does one be an excellent person online ? What does it mean to own an online persona, outright, independently, with alodial title ? How does one signify, to leave one's mark online ? How does one identify online ?
From The V Manual Genesis, we establish the definition of identity :
Identity is constructed, upon a fixed support*, by others' view.
--
* The best implementation of that "fixed support" currently known is provided by asymmetric key ciphers, but it's altogether unclear whether a better implementation could, at least in principle, exist.
From that von Mises adnotation, ownership is defined.
An owner is correctly defined as he who may exclusively destroy an economic good... Once the owner is the only one able to destroy the good, his refrain from destruction then entitles him to demand the full price in exchange.
Why are asymmetric key ciphers the best fixed support implementation ? What makes them economical to own, in the proper sense ?
Asymmetric key ciphers are the most economical form of online identity because securing them depends on using pieces of secret information that adversaries cannot predict. Thus, if you can learn to keep a secret with computers, you, dear reader, can learn to own an online persona.
For sound money settlement network necessities, the work continues to prove Bitcoin to be the most economical to own and Peer.
For broader online identity and communication necessities the state of the art fixed support is the RSA algorithm and the infrastructure for others' view is the Web of Trust.
RSA's(i) security is based on the computational intractibility of factoring large numbers. For example, which is harder, finding the factors of 13`843`867 or multiplying 2`029 and 6`823 ? If I just gave you the first number, it'd likely take you a while to find its factors, but if I give you the last two with a paper and pen and ask for their product, you can probably get the result in less time than it takes to drink an espresso.
These days,(ii) to generate a strong and practical RSA key pair, the smooth operator uses natural randomness and sharp software to pick two 2048 bit prime numbers to form the secret key. The software exposes the operator to the secret key and the 4096 bit(iii) public key. As long as the operator keeps the secret, he can issue unforgeable signatures his peers can economically verify and his peers can encrypt messages only he can read.
If that didn't sink in, let me embolden, emphasize and underline that it means if you know what you're doing, all the AI bot armies in the world combined, plus all the other computing on top of them don't have enough compute to forge(iv) your identity and all the governments in the world plus all the corporations combined lack the power to decrypt your messages. That's what the stakes are, that's what keeping a smart secret affords you. Let that sink in.
The Web of Trust (WoT) is the interface for interacting with the wider world. RSA keys can be useful for encrypting data to oneself,(v) but their potential value is orders of magnitude greater when used with others. It works by users registering their keys in a database. Then, through interaction with other users of the system, ratings can be sent and received. Ratings range from 10 to -10 and can be accompanied by an optional comment. Trust isn't in the ratings or the web, trust is within oneself. What the ratings communicate is how well the rater can describe the ratee. The WoT works by reducing the unknowns problem.(vi) It allows the user - any user - to confidently identify the sources of information, both in the negative and in the positive.
When meeting someone new, the user is able to check if anyone else he knows has already given the newbie a rating and cross reference the claims of the newbie with the people he already knows without any input of the newbie. While keys are relatively cheap to create, they accumulate value and reputation with usage across time(vii) and the more value accumulated in a key, the more expensive it is to replace. Thus, if the actors are rational, it becomes economical to engage in deals with people that are worth less than the value of their reputation because delivering on the deal makes more sense than suffering a negative rating and burning their WoT identity and needing to start from scratch.
The WoT is an immune system against spies, scammers and bots.(viii) The dual function of encryption and signing from a single key allows unforgeable, signed contracts that can be kept private between the parties for as long as the deal goes well. For as long as the deal goes well, it can remain as private as long as the parties desire. If the deal goes sour, the aggrieved party can publish the contract as proof to support the negative rating he issues. WoT ratings can be thought of as a more efficient word of mouth. Consider the case where you get scammed. With word of mouth, you get around to telling ten of your friends to give them a heads, but you run out of time to tell the eleventh and he gets scammed by the same guy. With the WoT, you publish your rating once, as long as your friends are smart enough to be using the system, there's little to no chance they'll also fall victim.
The ratings are fundamentally subjective and depend on who the rater is. Positive ratings aren't necessarily good and negative ratings aren't necessarily bad. For example, if someone new to me already has a negative rating from someone I know is an idiot,(ix) it may be a good sign as those raters are contrarian indicators from my point of view. The point of the WoT isn't to make your judgements for you, but to provide you leverage for more efficient and effective judgements.
The WoT is not a new idea on the Internet, it's in fact one of the older ones. The first, crude implementation was described by Phil Zimmerman in Pretty Good Privacy (PGP) v2, first published in '92, to whit :
As time goes on, you will accumulate keys from other people that you may want to designate as trusted introducers. Everyone else will each choose their own trusted introducers. And everyone will gradually accumulate and distribute with their key a collection of certifying signatures from other people, with the expectation that anyone receiving it will trust at least one or two of the signatures. This will cause the emergence of a decentralized fault-tolerant web of confidence for all public keys.
Thus, it's older than the Web you're more familiar with, the WWW, which was published in '93. That you're unfamiliar with the WoT is a reflection that you've not made it very far outside of AOL, or whatever Silly Con Valley is calling it now, facegram, twatter, instaspace, noise, whatsbook, kinkedin, youhub, what have you, the poisonous platforms that exist first and foremost for their real clients : the corporations that keep them running with advertising buys and the governments that use them to run their psyops.
An early innovator in Bitcoin called nanotube, came along and implemented a WoT with a more expressive ratings scheme ranging from -10 to 10 with an optional comment. This was a key piece of infrastructure in the nascent Bitcoin economy that supported OTC trade before exchanges were widely available as well as Bitcoin investments.(x) The failure to maintain and spread the WoT has been the biggest drag on Internet freedom.
If freedom on the Internet is something you want for yourself, I have two options to recommend : the JWRD WoT and Eulora2.
The JWRD WoT is provided by JWRD Computing. It's implemented over IRC and, uses RSA keys in the PGP format.(xi) Connect to the IRC server using this guide. If you need help, ask.
Eulora2 is the masterclass in economy masquerading as a computer game. Eulora2 is implemented over a custom communications protocol and uses RSA keys in the VaMP format. That it's a game probably makes it the best entry point for learning and practicing the concept.(xii)
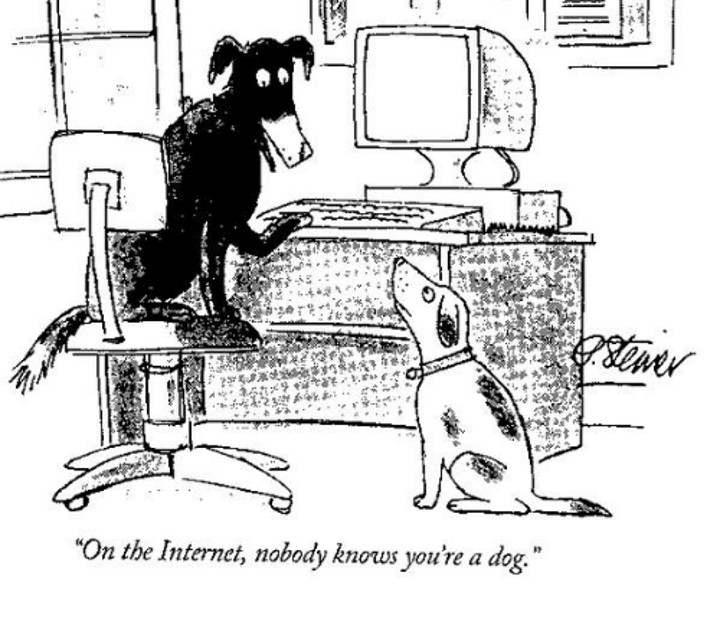
As the AI bot army of deep fakers grows stronger by the day, your ability to carry on with the Silly Con Valley status quo diminishes. If you manage to generate and secure an RSA key pair, you'll own your own persona. If you never manage, you'll forever be a peasant, accessing the online world only with your overlord's permission and filtered by what's most profitable for said overlords. Your challenge, my dear reader, is the same as it was in '93 and forever will be : no one knows you're a dog online.
Are you going to continue being a dog, collared by the platform owners and lead by their leash ? Or are you going to learn to be your own person ? It's up to you and fortunately it's not rocket surgery. Learning is not compulsory. Neither is survival.
- Invented in 1977 by Ron Rivest, Adi Shamir and Leonard Adleman. [^]
- As of Bitcoin blockheight=939039 work=85394136373600704532580524960 [^]
- Do you appreciate how big of a number this is ? 2^4096 is ~3.23 x 10^1233 which is a number with 1234 decimal digits. The estimated number of atoms in the observable universe is in the 10^80 range. [^]
- I hear the kids are calling it "deep fakes" nowadays. [^]
- For example, your Bitcoin wallet or password manager. [^]
- As observed with some regularity, there's a major difference between the unknowns we know we don't know, and the unknowns we don't know we don't know. [^]
- Time is a measurement of entropy. [^]
- You can meet humans in meatspace and exchange keys. That strengthens your understanding of who they really are and increases your confidence you're communicating with them over the wire. AI agents aren't meeting you for espresso. [^]
- e.g. Luke-Jr, gmaxwell, sipa [^]
- S.DICE and S.MPOE were two of the most valuable companies in Bitcoin history and were structured on top of the WoT. [^]
- We're planning to add support for VaMP keys too. [^]
- To me, one of the most interesting aspects of this game apart from the WoT is it's pro-automation by nature. While many games try to ban bots, Eulora2 comes with a bot out of the box. As I've been focused on writing this article, my character has been doing some valuable activities. When I go to sleep later, it'll be doing other valuable activities. Compared to other games, the value I create for myself in Eulora2 is more related by my ability to think strategically than my reflexes in mashing the keyboard. [^]